Applies to: Windows Server 2012 and 2012 R2
In a previous article, we demonstrated the steps needed to configure HA for the RD Connection Broker servers in an RDS 2012 farm. If you are using an RD Gateway server for a farm where HA is configured for the brokers, there are a few steps you will need to do in order for users to be able to successfully connect through the RD Gateway server(s).
When a user connects through the RD Gateway server, the gateway server will initially connect the user to one of the RD connection broker servers in order for the broker to determine what server or desktop the user will be connecting to. When HA is enabled for the farm, the gateway server will try to connect the user to the brokers using the DNS Round Robin name when HA was configured for the farm. By default, the DNS name used is not on the gateway’s allowable resource list for users to connect to. So for any user trying to connect to the farm through the RD Gateway, their access will be denied. To get around this, we will simply need to add a new resource authorization policy which will users to access resources through the gateway server using the designated DNS round robin name.
**Note – The following assumes a RD Gateway Connection Authorization Policy (CAP) is already configured on the RD Gateway server.
- From your RD Gateway Server you will need to create a new Remote Desktop resource authorization policy (RD RAP) with an RD Gateway-managed group that includes the DNS Round Robin name of the RD Connection Broker servers. From within server manager in Remote Desktop Services node, right-click on the RD gateway server and launch the RD Gateway Manager. (If this is being done from a server other than the Gateway server, please ensure the RD Gateway Management Console is installed on the server)
- From the RD Gateway Manager console, right-click Resource Authorization Policy and select create a new policy. Choose the custom option.
- When the policy opens, name the policy.
- On the User Groups tab, add the user group which will be accessing the resources. Here we added domain users. In environments with greater security requirements, a different security group should be used.
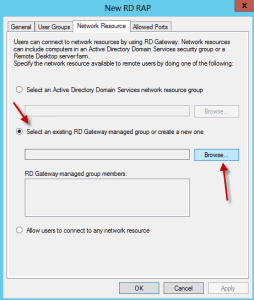
- On the Network Resource tab, select the option “Select an existing RD Gateway-managed group or create a new one”. Then hit the browse button.
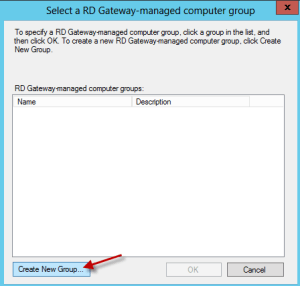
- When the screen appears, hit the Create New Group button.
- Name the new Group, then go to the Network Resources tab.
- On the Network Resources screen, enter the FQDN of the DNS round robin name used when creating High Availability for the broker servers. For our example, we used RDFarm.demolab.int. Hit the Add button.
- Once added, hit OK.
- Hit OK on the remaining screens to exit.
With the steps completed, the new resource authorization policy (RAP) will allow users to connect through the RD Gateway server to the farm that is configured with HA for the broker servers.
**Note: Please make sure the SSL certificate used for single sign on and publishing on the RD Connection Brokers matches the DNS name used to round robin the broker servers. For this example the SSL certificate name should reference the name rdfarm.demolab.int and should be installed on each of the RD Connection Broker servers. A wildcard certificate can be used to make things a bit simpler.
© 2014 Eddie Kwasnik “the Wolf” All Rights Reserved









#1 by Aron on June 25, 2014 - 9:20 am
Great article. Any reason not to install RD Gateway on the same server as the RD Connection Broker?
#2 by Eddie Kwasnik on June 26, 2014 - 9:48 am
Aron,
Technically, you can install the RD Gateway on the broker server. This should be done more so if it is for a test environment. If it is for a production environment, it is better that it is running on its own server. This is more so from a security stand point vs. a technical one.
Eddie
#3 by Aron on July 14, 2014 - 7:35 pm
Hi Eddie, i ended up using a separate RD Gateway server but when i connect externally it seems to pass me off to the desktop of a CB server instead of an SH, incidentally the published desktop in RDWeb works great. Any ideas?
My setup is
1 RDGW/RDWeb (RAP policy is configured as article above)
2 RDCB using HA
4 RDSH servers
#4 by Eddie Kwasnik on July 16, 2014 - 7:37 pm
Thats strange. Can you send me a screenshot of the connection from Server Manager (RDMS)?

Also, is it showing you are connected to a specific broker or the DNS round robin name you used for HA?
Thanks,
Eddie
#5 by Scott Bentz on August 21, 2014 - 2:32 pm
I know this is kind of late. I had this problem and just ended up putting my CBs in drain mode until I fixed the issue. My issue was how we had it networked. I ended up setting a SH farm name in DNS and having our users connect to that farm name using the gateway we setup. Hope this helps.
#6 by Sean on December 29, 2014 - 9:43 pm
Hi Eddie,
Just to follow up on this question: are there any security implications by deploying RD Gateway, Connection Broker, and Web Access on the same server?
I’m looking to deploy an HA Connection Broker solution with external access via RD Gateway, but would love to save on costs by not having to separate the CB and Gateway onto separate machines.
Thoughts? Is this a dangerous solution for a production environment?
#7 by Eddie Kwasnik on December 31, 2014 - 9:28 am
If at all possible, I would recommend leaving the Broker inside your network. Its more secure and part of Microsoft’s best practices. Are you able to use virtual servers to handle this? Plus, if you were to setup HA for the brokers, then you would have to put a firewall rule in place for the brokers to connect back to SQL.
#8 by DVelardo on October 21, 2014 - 2:17 pm
Great article! If we are using load balancers instead of DNS Round Robin, would we simply use the VIP of the balancers in place of the DNS name when configuring the Remote Desktop resource authorization policy?
#9 by Eddie Kwasnik on October 21, 2014 - 2:26 pm
That is correct. Just use the FQDN you are using for the VIP in your RAP on the RD Gateway.
#10 by BryanQ on January 19, 2016 - 6:28 pm
I have multiple unique sets of Terminal Server farms which are accessed via 2 load balanced RDS Gateway servers. Presently we are only using 1 TS as the broker and looking to add the rest of the TS’s in each farm as a Broker for their farm. Most of the unique farms have 2 Terminal servers, but I also have some with 3 and soon to be some with 4 Terminal servers. I was looking to place the DB for each of the Terminal Server farms on the same Server with SQL and then also HA the SQL Server so that it is not a single point of failure. Is this a doable solution and what should I have in consideration for this type of setup.
Each of the Terminal Server farms has a back-end SQL 2012 Standard server which could be an option to place the DB for the Broker servers, but if it could be avoided we don’t want to have this HA Broker DB compete for resources with the application which is presently using the SQL server by itself.